National Cyber Security Month: Week 2
Its week two of National Cyber Security Month! This week Toby talks you through the risks and what you can do to avoid them!
With so many of us using a multitude of connected devices day in day out, those with malicious intent employ a wide variety of methods that you need to look out for:
Phishing
Phishing is when a bad actor impersonates a legitimate company as a means of getting you to fill in personal information.
This is usually in the form of an email that looks like it comes from a legitimate and trustworthy source such as Microsoft or HMRC and will usually prompt you to click on a link to login with your details. When you click on the link you will be taken to a website that looks like the real thing, but which is actually a copy that will harvest any details that you enter into it.
To Avoid being caught out:
- Check all email for spelling/grammatical errors.
Phishing emails are often sent from non-native speaking countries and so may contain mistakes that an official communication would not. - Hover over links in the email before you click them
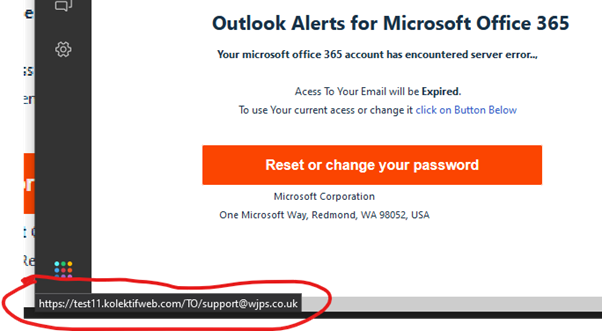
If you hover your mouse over links in the email, a box should pop up giving the address that it will go to: - Check the email address of the sender
Does it match the content of the email? Is it unnecessarily complex?
Do you think this email below is legitimate?
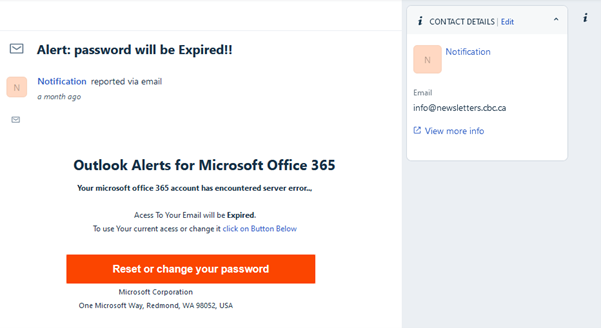
It’s not!
Here are some giveaways:
- Email address inconsistent with the content ([email protected]) – emails from Microsoft would likely end in ‘@microsoft.com’ or ‘@office.com’.
- Spelling/Grammar mistakes: ‘Access’ is consistently misspelt, ‘Microsoft Office’ not capitalised.
- Odd phrasing: ‘To use Your current access’ – likely written by a non-native English speaker.
- Hovering over link gives a strange website address (definitely not a Microsoft website!)
Viruses
Viruses are malicious files that can wreak havoc on your computer and potentially delete or corrupt your precious documents.
Usually a virus will get onto your pc via a file that you’ve downloaded – similar to phishing, the sending will often rely on tricking into downloading it usually from an email attachment or website disguised as a legitimate source. Viruses take many forms, Two of the most common are so-called ‘Ransomware’ which will lock up all your files and the scammer will then demand payment before they will release them and ‘Spyware’ which will remain hidden on your computer and secretly log your activity (such as key presses) so that criminals can watch you type out passwords.
The best defences against viruses are:
- Install a respected anti-virus product and ensure that it’s kept up to date.Newer versions of Windows now include ‘Windows Defender’ which should automatically identify and quarantine any suspicious files.
- NEVER download and open any email attachments unless you are 100% sure that the sender is legitimate.
- Keep your operating system up-to-date.
Updates to Windows and Mac often fix security exploits that attackers can use to get in to your system.
Phone Scams
Phone scams are similar to phishing in that you will usually get a caller who will try to appear legitimate (often claiming to be from Microsoft Support or HMRC) who will then try to engineer a situation where you give over your password details, or give them control of your computer so that they can lock up your files and demand money.
To avoid being caught out by scammers:
- NEVER give out your password or personal information to anyone calling that you didn’t expect.
- If in any doubt about the authenticity of a call – hang up and ring the company back on their publicly available phone number.
- NEVER allow an unexpected caller to guide you into doing anything on your computer.
- If you are asked to wire money, or buy gift cards this will be a scam – hang up immediately!
- Sign up to the Telephone Preference Service.
It can be intimidating, the sheer number of ways that scammers and criminals can use to target you in the online world, but knowing how to deal with these risks and keeping your wits about you when on the computer, or on the phone will go a long way into helping you protect your money and your data.
Published: 11/10/2021 Published by: WJPS
Return to News Page.